My previous post was about RouterOS Mac-Telnet application for Linux users where I talked about the MAC-Telnet client I created for Linux users.
Since then, I have both started porting it to OS X and to create a daemon version of MAC-Telnet, called “mactelnetd”. You can look at the different branches at github.com.
To use mactelnetd, install MAC-Telnet from the github link, using either the latest .deb file from the download section (if you are on Ubuntu or Debian), or download the sources and compile it yourself. You can find instructions for this on my previous post. you first need to edit the /etc/mactelnetd.users file. This file consists of the users and their respective passwords for logging into the server. I wish we wouldn’t have to write the passwords in plain text, but the authentication method used in the mac-telnet protocol demands that we know the actual password, unlike ssh/regular telnet, where the password can be stored as a hash sum.
The format of /etc/mactelnetd.users is like this:
# Users file for MAC-Telnetd
# Use existing usernames from your system
#
# Format:
#username:password
haakon:mypass |
# Users file for MAC-Telnetd
# Use existing usernames from your system
#
# Format:
#username:password
haakon:mypass
Here I have activated the user account haakon, with apssword “mypass”. It is important that the user names that you enter into this file is existing user names from your Linux machine. The mactelnetd daemon will check /etc/passwd for home directory, and what shell to spawn for the user, as any regular terminal server.
When you have created/modified this file to your wishes, you can start the server daemon:
If there were no error messages, it spawned successfully and you can watch it’s log entries via syslog.
$ tail -f /var/log/syslog
Dec 26 01:06:08 haakon-kontorpc mactelnetd[10183]: Bound to 0.0.0.0:20561
Dec 26 01:31:17 haakon-kontorpc mactelnetd[10183]: (28780) New connection from 0:c:42:3e:20:c2.
Dec 26 01:31:17 haakon-kontorpc mactelnetd[10391]: (28780) User haakon logged in. |
$ tail -f /var/log/syslog
Dec 26 01:06:08 haakon-kontorpc mactelnetd[10183]: Bound to 0.0.0.0:20561
Dec 26 01:31:17 haakon-kontorpc mactelnetd[10183]: (28780) New connection from 0:c:42:3e:20:c2.
Dec 26 01:31:17 haakon-kontorpc mactelnetd[10391]: (28780) User haakon logged in.
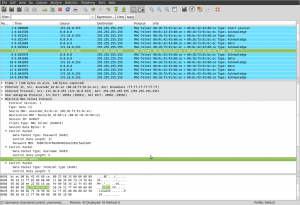
Here you see the results of me logging into my Linux Desktop machine from a MikroTik Router using the RouterOS command “tool mac-telnet 1c:6f:65:2c:98:b7”
[admin@Holmenveien] > tool mac-telnet 1c:6f:65:2c:98:b7
Login: haakon
Password:
Trying 1C:6F:65:2C:98:B7...
Connected to 1C:6F:65:2C:98:B7
Linux haakon-kontorpc 2.6.35-23-generic-pae #41-Ubuntu SMP Wed Nov 24 10:35:46 UTC 2010 i686 GNU/Linux
Ubuntu 10.10
Welcome to Ubuntu!
* Documentation: https://help.ubuntu.com/
haakon@haakon-kontorpc:~$ w
01:32:52 up 24 days, 22:48, 2 users, load average: 0.53, 0.61, 0.57
USER TTY FROM LOGIN@ IDLE JCPU PCPU WHAT
haakon tty7 :0 01Dec10 24days 26:29m 3.17s gnome-session
haakon pts/0 0:c:42:3e:20:c2 01:32 0.00s 0.15s 0.00s w |
[admin@Holmenveien] > tool mac-telnet 1c:6f:65:2c:98:b7
Login: haakon
Password:
Trying 1C:6F:65:2C:98:B7...
Connected to 1C:6F:65:2C:98:B7
Linux haakon-kontorpc 2.6.35-23-generic-pae #41-Ubuntu SMP Wed Nov 24 10:35:46 UTC 2010 i686 GNU/Linux
Ubuntu 10.10
Welcome to Ubuntu!
* Documentation: https://help.ubuntu.com/
haakon@haakon-kontorpc:~$ w
01:32:52 up 24 days, 22:48, 2 users, load average: 0.53, 0.61, 0.57
USER TTY FROM LOGIN@ IDLE JCPU PCPU WHAT
haakon tty7 :0 01Dec10 24days 26:29m 3.17s gnome-session
haakon pts/0 0:c:42:3e:20:c2 01:32 0.00s 0.15s 0.00s w
If you want to shut down the mactelnetd server, simply write “sudo killall mactelnetd” in your shell.
FUN TIP: If you want “fancy” terminal promt like RouterOS has, with syntax coloring on your Linux machine (logging in via console, xterm, ssh or mactelnet), you can install the shell “fish“, and then change your user settings to use it as the default shell by issuing:
$ sudo usermod --shell /usr/bin/fish myusername |
$ sudo usermod --shell /usr/bin/fish myusername
NB: Be sure that the file /usr/bin/fish exists, and change “myusername” with your username, and remember to test logging into a second console, just to be sure you did this correctly, before logging out of your current terminal. To revert, set /bin/bash as your shell again, or what ever shell you previously used.
Here’s a direct link to the latest Ubuntu/Debian package at the time of writing:
mactelnet_0.2-1ubuntu1_i386.deb